Authorization in Windows 10 by entering a password is one of the mechanisms for protecting your computer and personal data. But having different passwords on each site, the user can easily confuse them and enter the wrong password to log into Windows 10. If
Read moreCleaning your hard drive of debris
Good afternoon, dear readers. Every computer user wants his device to always...
192.168 1.1 login to the router. Setting up a router - how to find out the password for the web interface. Trying to access the wrong router address
http://192.168.1.1 is a login to your router’s personal account via a web interface from manufacturers such as...
Self-configuring a universal remote control for a TV. Password for the universal remote control.
A remote control (remote control) is an incredibly convenient thing, and it’s unclear how we lived before without them? With its advent, we have one less problem, although sometimes another, no less important one arises - how to set up the remote control? How
Read moreWindows phone forgot password on phone
Out of the box, Windows Phone smartphones have plenty of ways to deny access to certain files. This is the Children's Room, useful if the Winphone sometimes ends up in the hands of small users, as well as the Application Corner - less limited in scope
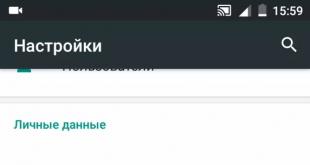
Read moreScreen lock on Android: how to set it up?
Every smartphone will definitely have files that the user wants to keep securely from prying eyes. These can be photographs, videos, personal notes or email correspondence. If a smartphone or tablet falls into the wrong hands, it could lead to...
Read moreThe best programs for encrypting information - TrueCrypt, VeraCrypt, DiskCryptor How to open a truecrypt encrypted file
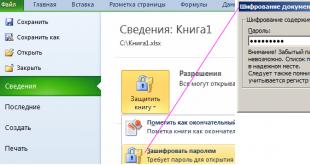
Excel allows you to use a password to restrict user access to documents at different security levels. There are 3 basic types of password protection for Excel files: Protecting the opening of a document. Protection against changes to data in a document. File encryption. How to bet
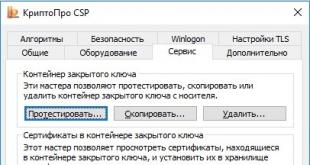
Read moreToken PIN: password with special rules
Tokens, electronic keys for accessing important information, are becoming increasingly popular in Russia. A token is now not only a means of authentication in a computer operating system, but also a convenient device for storing and presenting personal information.
Read moreThe company "maximum" produces seals and stamps - questions about digital signature
This page contains answers to frequently asked questions that arise when working with digital signatures. Select the question you are interested in, open it and strictly follow the instructions. WOscripts.com - JavaScript - Contractible Headers Script 1. Obtaining digital signature To obtain
Read moreWhat is the default Samsung password on your phone?
Posted 12/20/2015 Because your Android device contains a lot of system and hardware information, it can be difficult for the average user to access. But if you know Android secret codes, then
Read moreRating of the best Chinese smartphones in terms of price-quality ratio High quality Chinese phones
The success of Chinese smartphones in the world no longer surprises anyone. Even despite the economic problems that have recently been observed in China, their smartphones are still produced in huge quantities and are displacing manufacturers of these devices from the rankings.
Read moreHow to flash a Windows smartphone: step-by-step instructions
In this article we describe returning to the original firmware. If you are looking for an article about hacking a smartphone, close the tab. If you have a Nokia Lumia 710 or 800, then instructions for installing custom firmware can be found. This instruction is suitable for any t
Read more